Tagi - interference
Like any tool, jammer can be used in many ways, both efficiently and inefficiently.Ships in Russian waters are disguised as inland airports, ships in Chinese ports are reported to be inland and maneuvering inside government buildings, and ships in parts of the world broadcast their positioning circles thousands of miles away in Northern California.
If they have become a problem in the workplace, employers can install GPS jammers to prevent them from causing problems.Mobile deterrent devices are widely used and have produced very positive results.Unfortunately, telling people to mute their devices is not going to work.Whatever the circumstances, a signal jammer can jam up the frequencies cells need to receive calls, preventing phones from ringing out (since the call won't come through, to begin with).
If employees cannot stop posting on social media sites or texting, this may be a good choice, rather than simply firing offending employees.It is a call-blocking device, which can avoid active call termination service.We can debate whether this speaks to some larger social problem, but it's still true anyway.By carefully selecting the location of signal jammers, it is even possible to block communications in critical areas of the facility rather than elsewhere.
While GPS jamming and fraud are problems in many areas of transportation and critical infrastructure, they are often most pronounced in maritime transportation.And then there are prisons, where unauthorized communication lines may help individuals promote crime while locked in.Most of the time, you'll find them in one place, and a phone call can be very disruptive because silence is an expectation.
The RF signal has a frequency similar to that used by the cellular carrier.The workshop is part of an effort by the federal government and an important part of educating the public about the pitfalls associated with over-reliance on GPA.Even funerals are not immune to the odd phone call that breaks the silence or prayers.This is more true for those working in various governments and prisons, but
signal jammer can block communications as this can be a severe security issue.
Cell phone jammers can prevent these calls from coming in the first place.While it is important to review local laws on this issue, there have been cases where individuals have installed jammers (usually cell phone jammers) to prevent interference.
The cell phone jammer will not only block the signal, but you can't make any phone calls, including 911 emergency calls.In February, President Trump issued an executive order on the use of current positioning, navigation and timing.Not to mention that they should never have had a cell phone in the first place.This is because automatic identification systems (AIS) used for collision avoidance and traffic management on large ships transmit position data based on GPS output.
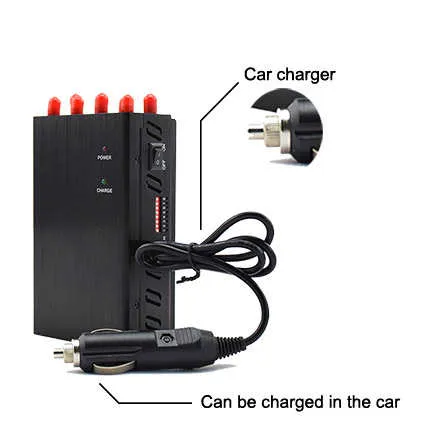
According to the product model, can be divided into large-scale jammers and portable drone jammer.There are always quite a few people who open their devices for some reason.If you are a government worker or contractor, don't forget to check our deals, which are designed to help you complete important work within your budget without sacrificing quality.
Large signal circuit breakers are mainly used in churches, hospitals, schools and other places.The United States Coast Guard lists GPS signal interference as an "Urgent problem" for the IMO.For example, some military facilities do not allow communication without prior approval.If the protective case is useful, it should be stored in a dry, well-ventilated place to avoid GPS interference and to prevent temporary exposure to salt spray and harmless gases.
Related articles
Solutions to mobile phone signal jammers in oil depots
Are car gps signal jammers useful?
Business secrets still require cell phone blockers
Within a certain frequency range, the mobile phone and the base station are connected by radio waves, and the transmission of data and sound is completed with a certain baud rate and modulation method. According to the above communication principle, the wifi jammers scans from the low-end frequency to the high-end of the forward channel at a certain speed during the working process. This scanning speed can form garbled code interference in the message signal received by the mobile phone, and the mobile phone cannot detect the normal data sent from the base station, so that the mobile phone cannot establish a connection with the base station. The mobile phone shows phenomena such as searching the network, no signal, and no service system. In the end, the mobile phone has no signal and cannot receive text messages or calls.
We can compare a mobile phone to a radio for the time being. The radio often appears to be buzzing or the channel is simply confused and cannot be heard. This means that the signal is interfered. Since the radio can be interfered, so can the mobile phone. of and by some device interference.
There are many different names for mobile phone signal jammer, jammers, mobile phone jammers, signal jammers, mobile phone signal jammers, mobile phone signal blockers, mobile phone isolators, mobile phone blockers, mobile communication signal jammers, mobile phone signals Degree shielding instrument, mobile phone jammer, signal jammer, mobile phone blocker, signal blocker, mobile phone signal isolator, signal isolator, mobile phone signal interceptor, radio signal jammer. The military jammer scans from the low-end frequency to the high-end of the forward channel at a certain speed during operation. This scanning speed can form garbled code interference in the message signal received by the mobile phone, and the mobile phone cannot detect the normal data sent from the base station, so that the mobile phone cannot establish a connection with the base station. The mobile phone shows phenomena such as searching the network, no signal, and no service system.
For the uplink and downlink channels of the mobile phone system, it uses frequency doubling, frequency division, frequency hopping filtering and other technologies to analyze the required shielding frequency; customize a spherical shielding space according to the power of the jammer, and automatically form a shielding magnetic field within the specified range , making mobile phones in this space invalid. When the jammer is in the working state, it can disable the signal receiving and sending functions of mobile phones within the specified range, making it impossible to dial out and dial in, so as to achieve the purpose of mandatory disabling.
The global positioning system (GPS), the space network that helps planes, ships and explorers orient themselves, could be disabled by gps jamming using cheap shop-bought equipment and information gleaned from the Internet, New Scientist magazine said.
The weekly said the U.S. Air Force formed a task force dubbed "Space Invaders" to look for weaknesses in the satellite communications and navigation system. The system is so popular now that even RVs and GPS watches use it for positioning.
Simulating a potential enemy, two novice technicians successfully assembled a satellite jammer GSM, relying on information downloaded from the Internet and materials purchased from general stores.
They assembled an ultra-high frequency (UHF) signal amplifier and noise generator for just $7,500. The device used copper pipes as antennas, plus some jumble of wooden blocks and plastic pipes, and was powered by an oil-fired generator.
They put the homemade device on an open pickup truck and turned it into a "signal cellphone jammer" that effectively blocked satellite dishes and the military's UHF receivers from getting the ultra-high frequency signals of the "Global Positioning System".
"Using a different component could interfere with GPS signals on other frequencies."
Related articles
How to calculate signal jammers shielding range
How to choose the most suitable cell phone signal jammers?
How to judge the quality of gps signal jammer
Signal Jammers Protect Your Personal Communication Devices
What are the advantages of high-power mobile phone signal jammers?
As the drone industry is taking off, some individuals and groups have started using drones for malicious purposes around the globe.The cell phone signal jammer gps in the school dormitory are mainly used at noon and evening when students are resting.More importantly, the mobile phone will spark during the dialing process, which can easily cause a fire and cause the gas station to explode.These mobile signal jammer are relatively cheap, disrupt communication on specific frequencies, and are mostly used for personal privacy and security reasons.The signal of the mobile phone will affect the normal operation of the equipment, resulting in inaccurate measurement.We've all seen news articles about drones being used for nefarious purposes and wondered if there was counter-drone technology to stop these actions.
Devices on a wireless network send and receive information using data packets at a specific frequency.When the cell phone battery starts, when the ringer rings, it can generate enough energy to cause a slight spark that can cause a fire.In a gas station, the driver used a mobile phone when refueling, which caused an explosion and caused a serious accident that caused many casualties.The gain of the project is that we are able to block communication coming into and going out from a GSM phone operating on the 890MHz to 960MHz frequency band.Obviously, the school's behavior is mild and does not affect students' freedom of communication and expression.Many anti-drone systems companies are following news stories about bad drones and flagging their products and/or services.Those who use GPS satellite signals for navigation in manned aircraft or cars, or those who use wireless frequencies such as Wi-Fi.
In some cases,satellite interference or solar flares can temporarily interrupt the transmission of GPS signals. The freedom of communication and speech that citizens enjoy in accordance with the Constitution and the law shall not exceed their due scope. Some students often use their mobile phones to surf the Internet in bed, and some even use their mobile phones to surf the Internet in the middle of the night. At present, the mobile phone signal is almost everywhere, and all electrical equipment is surrounded by it. However, gps blocker differ in that they transmit radio signals or signal noise at the same frequency as GPS devices to clip or distort GPS satellite signals. The answer is that there is counter-drone technology, which has been in the military for years, but the question is how to legally use counter-drone technology outside of war zones without causing all kinds of confusion.
The receiver relies on these precise and specific satellite signals to determine its position in the world. In recent years, with the rapid development of mobile phones, it is not uncommon for students to use mobile phones to affect their life and learning. When using a mobile phone, there is data exchange between the mobile phone and the base station, and random mutation signals are generated, so that a dynamic electromagnetic field is formed around the electrical equipment.
The simulation result and practical result were studied and they were found to be approbatory equal. Once the tracker receives signals from four or more satellites, it determines its position through a series of time calculations and trilateration. A signal jammer can be a hand-held, portable device that prevents wireless communications within a 15-meter radius. The wifi blocker gps can be big or small, and there are many channels in any frequency band of mobile communication. The GPS tracking device then transmits this location and speed information to the monitoring site, usually over a cellular network. When the mobile phone signal amplifier is not used, the interference of the surrounded signal to other electrical equipment is minimal.
Related articles
Cellular Signal Jammer Circuit Related Search Information
Internet Signal Jammer Amazon Related Search Information
Signal Jammer Map Related Search Information
Wi-Fi jammers: The tool of choice for criminals
The use of Wi-Fi jammers in burglaries is on the rise, indicating a growing trend among burglars. To counteract this, the police have taken proactive measures by securing arrest warrants to thoroughly investigate and apprehend those involved.Exploiting vulnerabilities present in wireless networks, thieves and criminal organizations are capitalizing on these weaknesses, while law enforcement agencies are actively pursuing these criminals by means of arrest warrants. By employing signal jammers, these perpetrators can effectively disable security systems and surveillance cameras, enabling them to clandestinely infiltrate homes without raising any red flags for the police.

Exploit wireless network vulnerabilities
Due to the extensive adoption of wireless networks in residential settings, perpetrators and criminal syndicates have discovered an alternative method to perpetrate illegal actions without legal permission. Exploiting the dependence of numerous home security systems and cameras on Wi-Fi connections for communication and surveillance, thieves take advantage of this vulnerability.This legal loophole was cleverly employed by the crew to evade the requirement of a search warrant. By utilizing Wi-Fi jammers, thieves can effectively disrupt these connections, rendering security measures useless without proper authorization.
Disable security systems and cameras
The presence of Wi-Fi interference raises apprehension as it allows thieves to tamper with the signals that security systems and cameras heavily depend on. By disabling these devices, criminals can carry out their illicit actions without the worry of being recorded or triggering any alarms.
By employing this technique, they gain a significant upper hand as they can enter the residence without alerting anyone or leaving any incriminating evidence, even in the absence of a search warrant. Moreover, it affords them a greater window of opportunity to act before authorities or homeowners become aware of the intrusion, without requiring a warrant.
The mechanism of Wi-Fi interference
Jamming wireless signal
Wi-Fi interference serves as a tactic employed by criminals to hinder or obstruct wireless signals, effectively preventing communication between devices connected to a Wi-Fi network. The radio frequencies emitted by these jammers can disrupt the seamless operation of the Wi-Fi network, resulting in its unreliability or complete inability to function.
Radio frequency interference
The functioning of jammers involves the transmission of radio signals on the same frequency band utilized by Wi-Fi networks. This interference hampers the smooth transmission and reception of data packets, thereby rendering it impossible for legitimate users to gain access to the network. Consequently, individuals attempting to connect to the targeted network will encounter severe connectivity problems or may find it completely unattainable.
Wi-Fi networks can be subjected to specific frequency bands through the use of different types of jammers. For instance, certain jammers are designed to operate on the 2.4 GHz band, which is commonly utilized by older Wi-Fi standards like 802.11b/g/n. On the other hand, there are jammers that can specifically target the 5 GHz band used by newer standards such as 802.11ac/ax.
By concentrating on specific frequency bands, criminals possess the ability to selectively disrupt devices or networks with certain capabilities and vulnerabilities. This strategic approach empowers them to exploit security system weaknesses, ultimately gaining unauthorized access to homes or businesses.
The invasion of organized crews and high-end homes
The tactics employed by organized crime syndicates to gain unauthorized access to homes are growing more sophisticated, with the utilization of Wi-Fi jammers for upscale break-ins. These criminal networks specifically set their sights on high-end residences boasting advanced security systems, deeming them as optimal targets to engage in illicit pursuits.
Through the utilization of Wi-Fi jammers, thieves can effectively evade alarm systems and surveillance cameras that would typically obstruct or capture their actions. This technology enables them to operate covertly, providing them with a substantial advantage over homeowners who depend on these security measures to ensure their safety.
These well-organized operatives employ a methodical approach when selecting their targets, often investing considerable time in conducting thorough research and surveillance beforehand. Their primary objective is to identify residences with valuable assets, such as precious jewelry or valuable artwork, to ensure that the potential rewards outweigh the inherent risks. Once a target has been chosen, they meticulously plan every detail to ensure a successful break-in.
There are situations where these wrongdoers may go to the extent of impersonating service personnel or delivery personnel to gain entry into a property. By mingling with authentic professionals, they can seamlessly penetrate a heavily guarded residence without raising any red flags.
It is imperative for homeowners to acknowledge this growing menace and take appropriate actions to ensure their safety and protect their property. Going beyond traditional alert systems, investing in additional layers of security can act as a deterrent to these organized criminals. For instance, the installation of motion sensor lights around the house or the use of smart locks that require biometric authentication can provide an extra level of protection against these resourceful wrongdoers.
Homeowners must prioritize staying well-informed about the latest techniques employed by criminals and maintaining a vigilant mindset to ensure the safety of their homes. By staying ahead of the game and implementing comprehensive security measures, homeowners can greatly diminish the likelihood of falling prey to these organized wrongdoers.

Opis
Posty: 346
Komentarze: 5
Perfectjammer Is A Professional Jammers Store, Main Business Is Various Types Of Jammers Wholesale And Retail, We Will Strive To Provide Your With Quality Product And The Cheapest Price.

Kategorie

Tagi